Contact Information
News

DAOs (Decentralized Autonomous Organizations): The Future of Digital Governance
- By James
- . 16 April 2026
The evolution of blockchain technology has introduced a revolutionary concept in how organizations are structured and governed—Decentralized Autonomous Organizations (DAOs). Unlike traditional organizations that rely

Entrepreneurship & Leadership: Building, Leading, and Scaling Successful Businesses in 2026
- By James
- . 16 April 2026
Entrepreneurship is more than just starting a business—it’s about solving problems, creating value, and building something that can grow and thrive. At the heart of

Software & SaaS Review: The Best Tools Powering Businesses in 2026
- By James
- . 15 April 2026
Software and SaaS (Software as a Service) platforms have become the backbone of modern businesses. From managing teams and automating workflows to handling customer relationships

Business & SaaS Tools Tutorial: How to Choose, Use, and Scale the Right Tools for Your Business
- By James
- . 15 April 2026
In today’s digital economy, businesses rely heavily on SaaS (Software as a Service) tools to manage operations, automate workflows, and scale efficiently. From project management

The Future of the Web: Trends, Technologies, and What to Expect in 2030
- By James
- . 15 April 2026
The web has come a long way—from static pages in the early days to today’s dynamic, interactive, and intelligent platforms. As technology continues to evolve,

AI Ethics & Regulation: Building Responsible and Trustworthy Artificial Intelligence
- By James
- . 14 April 2026
Artificial Intelligence (AI) is transforming industries at an unprecedented pace—from healthcare and finance to marketing and cybersecurity. However, as AI systems become more powerful, concerns

Identity & Access Management (IAM): Securing Digital Access in a Connected World
- By James
- . 14 April 2026
As businesses become increasingly digital, managing who has access to systems, data, and applications is more critical than ever. Identity & Access Management (IAM) plays
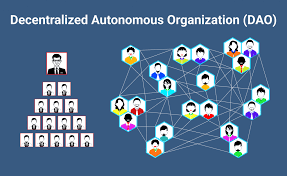
DAOs Explained: The Future of Decentralized Organizations and Governance
- By James
- . 14 April 2026
The rise of blockchain technology has introduced a new way of organizing people, managing resources, and making decisions—Decentralized Autonomous Organizations (DAOs). Unlike traditional organizations, DAOs

Digital Transformation: How to Future-Proof Your Business in the Digital Age
- By James
- . 13 April 2026
In today’s rapidly evolving business landscape, staying competitive requires more than just traditional strategies. Companies must embrace digital transformation to improve efficiency, enhance customer experience,

Gadgets & Devices Review: The Best Tech Innovations You Should Consider in 2026
- By James
- . 13 April 2026
Technology continues to evolve at a rapid pace, introducing smarter, faster, and more efficient gadgets into our daily lives. From high-performance smartphones and lightweight laptops

