Contact Information
Tech Digital Minds
Top Stories
ALL TOP STORIES
Gadgets & Devices Review: The Best Tech You
- . 7 April 2026
- 1 Views
-
Shares

2025: Current and Emerging Trends in Malware
- By James
- 288 Views
Understanding the Landscape of Remote Access Trojans and Malware in 2025 In the evolving world of cybersecurity, Remote Access Trojans (RATs) and Trojans remain central

HHS Unveils Version 3.6 of the Updated HIPAA Security Risk Assessment Tool
- By James
- 372 Views
The Latest Update to the Security Risk Assessment Tool: What You Need to Know The landscape of healthcare technology compliance is constantly evolving, making it

CISA Urges Agencies to Tackle ‘Major Cyber Threat’
- By James
- 359 Views
Navigating CISA’s Emergency Directive: Addressing Vulnerabilities in F5 Devices The cybersecurity landscape continues to evolve as threats become increasingly sophisticated. Recently, the Cybersecurity and Infrastructure

Age Verification Shouldn’t Transform into Data Collection by Another Name
- By James
- 213 Views
Understanding the Social Media Minimum Age Act 2024 and Its Implications With the Social Media Minimum Age Act 2024 coming into effect on 10 December

CHINA FOCUS: Mature Governance Takes Center Stage
- By James
- 346 Views
The Maturing Landscape of Data Compliance and Cybersecurity in China China’s once-sizzling market for data compliance and cybersecurity law has experienced a notable cooling, as
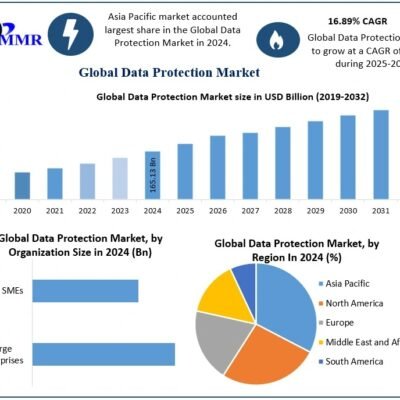
Data Protection Market Expected to Surpass USD 575.50 Billion by 2032 Amid Growing Cybersecurity Threats
- By James
- 304 Views
Understanding the Data Protection Market: Insights and Trends As businesses increasingly navigate a digital landscape replete with data challenges, understanding the data protection market becomes

New Era | Data Privacy: Compliance is Now Essential
- By James
- 164 Views
Navigating the Complex Landscape of Data Protection in Bangladesh The Value of Personal Data in the Modern Economy In today’s interconnected world, personal information is

Amazon Raises Concerns as Nation-State Actors Combine Cyber Intrusion with Physical Attacks
- By James
- 261 Views
Cyber-Enabled Kinetic Targeting: The New Battlefield Dynamics Recent investigations by Amazon’s threat intelligence teams have unearthed a profound evolution in how nation-state actors conduct warfare,

Constella Intelligence Recognized as Top Performer in Javelin Strategy & Research’s 2025 Dark Web Threat Intelligence Vendor Scorecard
- By James
- 247 Views
The firm achieved “Category Leader” status in all five evaluated categories, recognized for its innovative approach to mapping threat actor infrastructure. Fremont, CA – November

Understanding Machine Learning: A Beginner-to-Pro Guide
- By James
- . 23 September 2025
- 918 Views
-
Shares

The Truth About Rug Pulls: How to Spot and Avoid Crypto Exit Scams
- By James
- . 29 July 2025
- 894 Views
-
Shares

5 Common Crypto Scams and How to Avoid Them
- By James
- . 29 July 2025
- 961 Views
-
Shares

Safeguarding Your Digital Fortress: Why Cybersecurity is Your Business’s Lifeline
- By James
- . 10 August 2024
- 1,410 Views
-
Shares
Recent News
ALL RECENT NEWS
How to Leverage AI for Business Automation: A Step-by-Step Guide
- By James
- . 24 May 2025
- 1,019 Views
-
Shares

Natural Disasters: The Unpredictable Threats to Security
- By James
- . 4 September 2024
- 1,323 Views
-
Shares

Quantum Computing Breakthrough: What It Means for Your Smartphone’s Future
- By James
- . 3 August 2024
- 1,374 Views
-
Shares

AI Revolution: How Artificial Intelligence Will Transform and Change the World
- By James
- . 12 July 2024
- 1,559 Views
-
Shares






