Contact Information
Tech Digital Minds
Top Stories
ALL TOP STORIES
Crypto Security & Scams: How to Protect Your
- . 10 April 2026
- 5 Views
-
Shares

Cybersecurity as a Compliance Essential: Safeguarding Consumer Data in Debt Recovery
- By James
- 360 Views
The Intersection of Cybersecurity and Debt Recovery: A Vital Dialogue Photo by Philipp Katzenberger on Unsplash In the landscape of debt recovery, the balancing act

DCM Services Appoints Curtis Rebelein as Chief Information Security Officer
- By James
- 352 Views
nico-smith / unsplash MINNEAPOLIS — DCM Services, Inc. (“DCMS”) announces a significant leadership change as it strengthens its commitment to cybersecurity. To further cement its
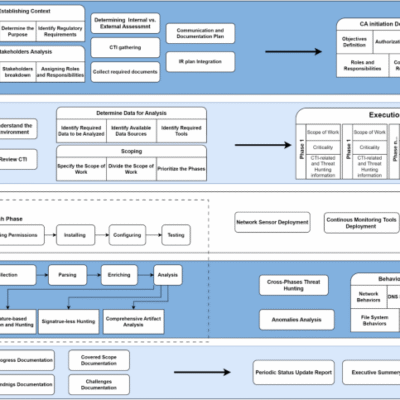
Proactive Detection of Cybersecurity Breaches Using the PROID Compromise Assessment Framework
- By James
- 329 Views
Unveiling the PROID CA Framework: A Standardized Approach to Compromise Assessment As the digital landscape continues to evolve, so do the complexities of IT environments.

Security Tools Review: The Best Cybersecurity Software to Protect Your Digital Life
- By James
- 33 Views
Security Tools Review: The Best Cybersecurity Software to Protect Your Digital Life

Weekly Recap: Salesforce Targeted by Hackers, CentreStack 0-Day Exploited
- By James
- 374 Views
Cybersecurity Weekly Roundup: Key Insights and Developments A Spotlight on Bug Bounty Strategies Navigating the complexities of bug bounty programs can often feel like a

FTC Unveils 10-Year Consent Orders on Information Security with Illuminate Education and Illusory Systems
- By James
- 126 Views
FTC Announces 10-Year Information Security Consent Orders with Illuminate Education and Illusory Systems In a notable move to enhance information security practices, the Federal Trade

Threat Actors Evolve: A Unified Operational Model Integrating Digital and Physical Threats
- By James
- 273 Views
In a rapidly evolving digital landscape, Amazon’s threat intelligence teams have made a startling revelation that intertwines digital operations with physical warfare. This emerging trend,

Introducing TruLens for Enterprise: Unified Threat Intelligence for TruRisk™ Management
- By James
- 369 Views
Navigating the Complex Cybersecurity Landscape: The Role of TruLens in Modern Threat Intelligence CISOs and security leaders today face extraordinary challenges amid an evolving digital

Resecurity and D4DS Join Forces to Enhance Advanced Cybersecurity Solutions in Saudi Arabia
- By James
- 130 Views
Resecurity and D4DS Join Forces to Enhance Cybersecurity in Saudi Arabia Date of Release: January 3, 2026 In an exciting development for the cybersecurity landscape

Understanding Machine Learning: A Beginner-to-Pro Guide
- By James
- . 23 September 2025
- 924 Views
-
Shares

The Truth About Rug Pulls: How to Spot and Avoid Crypto Exit Scams
- By James
- . 29 July 2025
- 901 Views
-
Shares

5 Common Crypto Scams and How to Avoid Them
- By James
- . 29 July 2025
- 968 Views
-
Shares

Safeguarding Your Digital Fortress: Why Cybersecurity is Your Business’s Lifeline
- By James
- . 10 August 2024
- 1,417 Views
-
Shares
Recent News
ALL RECENT NEWS
How to Leverage AI for Business Automation: A Step-by-Step Guide
- By James
- . 24 May 2025
- 1,025 Views
-
Shares

Natural Disasters: The Unpredictable Threats to Security
- By James
- . 4 September 2024
- 1,329 Views
-
Shares

Quantum Computing Breakthrough: What It Means for Your Smartphone’s Future
- By James
- . 3 August 2024
- 1,383 Views
-
Shares

AI Revolution: How Artificial Intelligence Will Transform and Change the World
- By James
- . 12 July 2024
- 1,566 Views
-
Shares






