In today’s digital landscape, cyber threats are no longer a matter of if but when. Businesses of all sizes face risks from ransomware, phishing, data breaches, and advanced persistent threats. This makes incident response and recovery a critical component of any cybersecurity strategy.
Having a well-defined plan can mean the difference between a quick recovery and devastating financial or reputational loss.
What Is Incident Response?
Incident response (IR) is the structured approach organizations use to detect, manage, and mitigate cybersecurity incidents.
It focuses on:
- Identifying threats quickly
- Containing damage
- Eliminating the root cause
- Restoring systems and operations
What Is Incident Recovery?
Incident recovery is the process of restoring systems, data, and operations after a security incident has been contained.
It ensures:
- Business continuity
- Data integrity
- System reliability
- Prevention of future incidents
Common Types of Cybersecurity Incidents
Phishing Attacks
Deceptive emails or messages used to steal sensitive information.
Ransomware
Malware that locks data until a ransom is paid.
Data Breaches
Unauthorized access to confidential data.
Distributed Denial of Service (DDoS)
Overwhelming systems to disrupt services.
Insider Threats
Employees or partners misusing access.
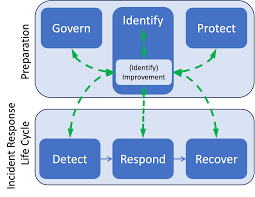
The Incident Response Lifecycle
A widely accepted framework is provided by National Institute of Standards and Technology (NIST).
1. Preparation
- Develop an incident response plan
- Train employees
- Set up monitoring tools
2. Detection and Analysis
- Identify unusual activity
- Analyze logs and alerts
- Confirm the incident
3. Containment
- Isolate affected systems
- Prevent further spread
4. Eradication
- Remove malware or vulnerabilities
- Patch affected systems
5. Recovery
- Restore systems and data
- Monitor for recurring threats
6. Post-Incident Review
- Document lessons learned
- Improve security policies
Key Components of an Incident Response Plan
Incident Response Team (IRT)
A dedicated team responsible for managing incidents.
Communication Plan
Clear internal and external communication strategies.
Documentation
Detailed procedures for different incident scenarios.
Tools and Technologies
Monitoring, detection, and recovery tools.
Essential Incident Response Tools
SIEM Systems
Platforms like Splunk help analyze logs and detect threats.
Endpoint Detection & Response (EDR)
Tools that monitor endpoint activities in real time.
Backup Solutions
Ensure data can be restored after an attack.
Firewalls and Intrusion Detection Systems
Prevent and detect unauthorized access.
Best Practices for Incident Response
Create a Clear Response Plan
Document every step of your IR process.
Train Your Team Regularly
Run simulations and drills.
Use Automation
Speed up detection and response times.
Maintain Regular Backups
Store backups securely and test them often.
Monitor Continuously
Use real-time monitoring tools.
Incident Recovery Strategies
Data Restoration
Recover from backups or secure storage.
System Rebuilding
Reinstall systems to eliminate hidden threats.
Security Hardening
Apply patches and strengthen defenses.
User Awareness Training
Educate staff to prevent future incidents.
The Importance of Business Continuity
Incident response is closely tied to business continuity planning.
A strong recovery plan ensures:
- Minimal downtime
- Reduced financial loss
- Faster return to operations
Challenges in Incident Response
Skill Shortages
Cybersecurity expertise is in high demand.
Evolving Threats
Attack methods constantly change.
Delayed Detection
Some breaches go unnoticed for months.
Complex IT Environments
Cloud, hybrid, and on-prem systems increase complexity.
The Role of Automation and AI
Modern cybersecurity relies heavily on automation and AI to:
- Detect anomalies faster
- Respond in real time
- Reduce human error
Platforms from companies like IBM integrate AI-driven threat detection into incident response workflows.
Incident Response for Small and Medium Businesses (SMBs)
SMBs are frequent targets due to weaker defenses.
Key Tips for SMBs:
- Use managed security services
- Implement multi-factor authentication (MFA)
- Keep systems updated
- Invest in affordable security tools
Legal and Compliance Considerations
Organizations must comply with data protection regulations such as:
- General Data Protection Regulation (GDPR)
- Industry-specific standards (HIPAA, PCI DSS)
Failure to respond properly can result in fines and legal consequences.
Future Trends in Incident Response
AI-Driven Security
Faster and smarter threat detection.
Zero Trust Architecture
Continuous verification of users and devices.
Cloud-Based Response Solutions
Scalable and flexible security tools.
Threat Intelligence Sharing
Organizations collaborating to fight cybercrime.
Final Thoughts
Incident response and recovery are no longer optional—they are essential for survival in today’s digital world. Organizations that invest in preparation, tools, and training can significantly reduce the impact of cyber incidents.
A proactive approach ensures not only faster recovery but also stronger defenses against future threats.
SEO FAQs
Q: What is incident response in cybersecurity?
It is the process of detecting, managing, and mitigating cyber threats.
Q: Why is incident recovery important?
It restores systems and ensures business continuity after an attack.
Q: What are the steps in incident response?
Preparation, detection, containment, eradication, recovery, and review.
Q: Can small businesses implement incident response plans?
Yes, even basic plans can significantly reduce risk.